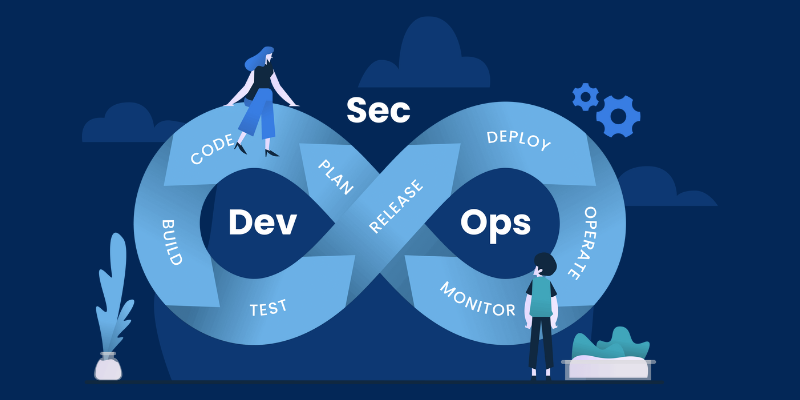
DevOps vs. DevSecOps: What’s the Difference?
DevOps and DevSecOps are two approaches to application development that may seem quite similar, but there is a significant distinction between them. What precisely differentiates DevOps from DevSecOps? How they impact IT, efficiency, and business performance depends on your team’s objectives. So, which strategy is best for your organization?
Some may view the difference between DevOps and DevSecOps as trivial, but this is not the case. Teams that understand how to distinguish between these two approaches will be better equipped to make key decisions that enhance efficiency within their development pipeline while also transforming current processes to emphasize speed, agility, and security.
What exactly does DevOps mean?
DevOps is a process aimed at increasing the speed at which software is developed and enhanced by leveraging continuous communication, automation, integration, and intelligence.
By emphasizing DevOps principles throughout the development cycle, developers gain better control over product infrastructure and can prioritize software performance over other goals.
DevOps objectives include:
- Boosting the speed of software delivery through automation and collaboration.
- Gaining greater control over production infrastructure.
- Prioritizing reliable and effective software delivery.
- Streamlining the integration of different software architectures and systems into both current and future products.
All these objectives are crucial for any developer or IT company.
It’s essential for any IT company to release high-quality products and software updates on time without frequent disruptions or delays. DevOps enables developers to focus on methodologies or systems that help them meet deadlines more consistently and reliably.
Read more: Boost the Software by Integrating AI into DevOps
What is SecOps?
Like its counterpart, SecOps combines two distinct concepts into a single acronym. As you might guess, “Sec” stands for security.
“Ops,” as in DevOps, refers to the operations or services of information technology. Therefore, SecOps refers to the focus on or approach to processes that enhance security throughout the development pipeline.
The objectives of SecOps include:
- Enhancing security by integrating cybersecurity at every stage of development.
- Maintaining security as an evolving and adaptive dynamic process.
- Allocating security responsibilities to stakeholders involved in creating and safeguarding a specific application.
SecOps focuses more on security than DevOps, which primarily concerns creating and continuously improving software and managing the development lifecycle.
Both approaches are essential for top-tier IT organizations today, especially given that cybersecurity is a significant concern for all enterprises.
What is DevSecOps?
This brings us to DevSecOps. If you’ve been following along, you can probably guess what this acronym represents.
- Dev = Focus on the software development pipeline and process
- Sec = Focus on software security and adaptation
- Ops = Focus on software operation and services
DevSecOps is essentially a combination of DevOps and SecOps, merging the two approaches to create a cyclical system that integrates practices from software development, cybersecurity, and technology operations.
The objectives of DevSecOps are to:
- Facilitate the rapid creation of reliable codebases and applications
- Align the prioritization of development efforts with security
- Encourage the use of a flexible framework and growth processes
- Ensure that security and development teams can collaborate and continuously improve
DevSecOps, like DevOps, comprises several essential components that are important to understand. Here’s a basic overview:
Because DevSecOps emphasizes automated development processes and integrates them with automated security measures, the goal of this methodology is clear.
DevSecOps involves implementing security policies early in the software development lifecycle and automating these procedures as much as possible.
By automating, standardizing, and shifting your security processes to the left, you will benefit from more agile development methods and combine the advantages of both methodologies.
Security Moves Leftward
In IT security, pushing your security duties to the left means transferring them to earlier phases of the development cycle.
By moving security to an earlier stage in the development pipeline, security processes and procedures are adopted before the application or software progresses too far to be adequately secured.
By adhering to this approach, development cycles can only proceed when codebases have been validated as securely as possible.
In essence, this protects IT organizations from encountering embarrassing security breaches or difficulties later in the development process that could have been discovered earlier.
Continual Feedback Loops
Equally important is the emphasis on continuous feedback loops.
By integrating these feedback loops, all development team members—including those responsible for raw development, security, and operations—are instantly updated on new features, policies, and development procedures.
Continuous feedback also ensures that automated processes continuously monitor the program for alerts or security vulnerabilities. With this process, real-time alerts or issues with the codebase as it is being compiled are both feasible and common.
This is one of the key factors that distinguishes successful DevSecOps teams from others, as it prioritizes collaboration and teamwork above all else.
Automated Security
Automated security is also a vital component for the continued operation of DevSecOps models and pipelines. By automating security, you reduce the likelihood of human error and ensure that security requirements are maintained with greater rigor and reliability.
Furthermore, by automating many of your security procedures or standards, your DevSecOps teams can accomplish more in less time. This is an excellent way to reduce costs and maximize available personnel.
Read more: Top 10 DevOps Trends to Watch 2022
DevSecOps Types
There are two main types of DevSecOps to consider:
Security as Code (SaC)
The primary objective of SaC approaches is to integrate security procedures into conventional DevOps principles, practices, and automated technologies. This is exemplified by performing fundamental infrastructure modifications and quickly testing for defects or security flaws.
This approach is entirely feasible if the DevOps team is aware of and aligned with these secure coding techniques, simplifying and increasing the efficiency of testing.
Infrastructure as Code (IaC)
DevOps approaches and methodologies also incorporate IaC. Thanks to virtualization and cloud computing, an increasing number of businesses can utilize software infrastructure managed services.
If you manage your infrastructure using configuration files based on code, you can often remove the complexity that conceals security vulnerabilities, making DevSecOps more feasible across the board.
Advantages of DevSecOps
Why should your team transition to DevSecOps practices? There are several potential benefits that you may notice immediately after making the switch.
Cost Reduction
By incorporating security early in their development cycles, many companies can save money.
This makes sense—by identifying security concerns early in the development lifecycle, you can implement fixes more quickly and with less effort, avoiding the need for costly security patches later on.
This is especially important for ensuring legal compliance with consumer safety.
For example, GDPR penalties can equal up to 4% of a company’s yearly earnings. The simplest way to avoid these costs is to ensure that you do not release an application with a clear security flaw.
Automated Security
By shifting security to the left of the DevSecOps pipeline, developers often benefit from automated security processes. This also benefits organizations and enterprises by freeing up personnel and enabling smaller IT security teams to do more with fewer resources.
Improved Knowledge of the Application
Although this might seem like a minor advantage, it is nonetheless essential. As DevSecOps integrates security into standard DevOps procedures, average developers will gradually become more familiar with security principles and naturally produce more secure code.
While integrating DevSecOps standards and practices may cause some growing pains, the potential benefits are well worth the effort.
What Do DevOps and DevSecOps Have in Common?
One way to compare DevSecOps and DevOps is by examining the fundamental components they share.
Collaborative Culture
Collaboration is crucial to the operations of DevOps and security teams, helping them achieve development goals such as quick iteration and deployment without compromising privacy. Both approaches bring multiple teams together to collaborate throughout the application lifecycle, ensuring effective outcomes.
Automation
Both DevOps and DevSecOps utilize automation in app development processes, often with the aid of AI. For DevOps, this includes tools like code completion and anomaly detection. In the context of DevSecOps, automated and continuous security checks and anomaly detection help proactively identify high-risk vulnerabilities and security threats, especially in complex and dynamic environments. This is particularly important when apps operate on distributed, multi-cloud infrastructures, and the IT perimeter extends to include identities.
Active Monitoring
Both DevOps and DevSecOps place a high value on data monitoring for learning and adaptation. Continuous collection and analysis of application data are crucial components of each approach, driving improvements. Access to real-time data is essential for optimizing application performance, reducing the attack surface, and enhancing the organization’s overall security posture.
Read more: The Importance of DevOps in Cloud Security Management
The Difference Between DevOps and DevSecOps
DevOps aims to provide a quicker and more efficient software deployment process. This is achieved by fostering collaboration between development and operations teams through shared KPIs (key performance indicators), ensuring that each team knows where it needs input to complete tasks without disputes or errors.
A good strategy includes automated technologies that enable DevOps engineers to release changes as soon as feasible while maintaining predictability in the end-user experience. However, DevOps teams don’t always prioritize preventing security risks throughout the process, which can lead to the accumulation of vulnerabilities that endanger applications, data, and other corporate assets.
The DevSecOps methodology departs from the usual “development and operations” strategy by incorporating security much earlier in each project’s lifecycle, even before any code is created. This innovative approach to software design integrates application assurance into every phase, from planning to deployment.
Engineers can ensure that applications remain secure during delivery, allowing users to have a safe experience whenever they use them. This strategy emphasizes implementing application security at the beginning of the build process rather than after the development pipeline. With this approach, a DevSecOps engineer ensures that applications are protected against threats before they are released to production and remain secure during updates. DevSecOps emphasizes that developers should write code with security in mind and addresses the security challenges that DevOps does not cover.
DevSecOps extends the DevOps ecosystem with additional capabilities such as code analysis, compliance monitoring, threat investigation, and vulnerability assessments. Incorporating these security standards into an agile framework ensures that the codebase remains secure through constant testing and assessment.
Which Activities Differentiate DevSecOps from DevOps?
DevOps opened the door for a new ecosystem of development and operations teams collaborating for a proactive SDLC (Software Development Life Cycle). While Waterfall and Agile approaches were linear and mapped project activities into separate sequential stages, DevOps enhances the SDLC by including methods such as:
- Continuous integration (CI) – Combines code modifications to ensure that developers can access the most recent version.
- Continuous delivery and deployment (CD) – Automates the process of providing updates to boost productivity.
- Microservices – Constructs an application from a collection of smaller services.
- Infrastructure as code (IaC) – Plans, implements, and maintains the infrastructure requirements of an application using code.
Here’s how it operates:
- Developers write the code and use version control to monitor any modifications.
- New code is included during the build step.
- Compilation and feedback from all code branches are obtained.
- The code reaches the deployment phase.
If all conditions are met, the code is released to production.
If errors are discovered, the developers correct the code, and the same procedures are repeated.
Each participant is accountable for the overall success of the software delivery process.
In contrast, the DevSecOps methodology includes the above techniques and adds:
- Enumeration of common weaknesses (CWE) – Improves code quality and boosts security during the CI and CD phases.
- Threat modeling – Incorporates security testing into the development process to save future costs and time.
- Automated security testing Regularly tests for vulnerabilities in new releases.
- Incident response management – Establishes a standardized response structure for security issues.
Read more: DevOps and Agile: How to Agile & DevOps Interrelated
How to Convert from DevOps to DevSecOps
Here are five steps that every business can take to enhance the security of its operations.
1. Collaborate with Developers to Tackle Security
Too often, developers see security as an obstacle, especially if it enters the process too late. Before making changes to your process, it’s essential to get teams on board with the DevSecOps philosophy. Ensure that everyone understands the necessity and benefits of securing applications early on and how this impacts your application development. Developers may not fully comprehend the specific security requirements and methodologies and might believe they can manage them independently.
2. Manage a Shift Left
The “shift-left” concept, where the responsibility for designing and implementing security is moved as early as possible in the software development and system design process, has proven to be a significant contributor to security improvement. Additionally, addressing issues in this manner ensures they are resolved permanently.
3. Select the Appropriate Combination of Security Testing Methods
Several security testing methods are available, and it can be challenging to determine which ones are best for your firm. Once you’ve identified how you wish to test security, the next step is to find the right tools for enforcing security.
4. Develop Coding Standards for Your Team
In DevSecOps, evaluating the quality of your code is a crucial component. Ensuring that your code is robust and standardized will make it easier for your team to secure it in the future. If you haven’t already, establish a mechanism for teaching developers coding best practices and ensure that code changes can be executed without disruption.
5. Secure Applications from the Inside Out
Rather than trying to protect the expanding perimeter, focus on protecting applications that operate in the public cloud from the inside out. This approach simplifies internal security strategies for IT staff, thereby enhancing your overall security posture.
Who Handles Security for DevSecOps Policies?
Does this mean developers must become security experts? Not at all. Most IT professionals understand that the majority of skilled workers are specialists to some extent.
This means that IT developers won’t necessarily need a comprehensive understanding of security procedures or be experts in implementing security measures.
Instead, most DevSecOps teams following these approaches will form a specialized team of security-focused IT or QA specialists. This smaller team’s responsibility is to identify vulnerabilities or potential entry points in a specific program.
After identifying these vulnerabilities, they can be reported to the development team, allowing them to patch the issues before they become a real problem.
DevSecOps Methodologies: Challenges and Solutions
This can lead to various challenges, particularly in communication.
Friction can easily arise between the development and security teams, especially if the development staff isn’t adequately trained or isn’t prepared to prioritize security over functionality or usability.
Implementing DevSecOps policies holistically is the best way to address these challenges.
By incorporating security into the company-wide or enterprise-wide development standards and keeping the development team informed, managers can reduce friction between development and security teams and ensure that everyone understands the broader mission objectives and associated risks.
Here are some examples:
- IT administrators can establish policies to eliminate poor coding practices.
- Managers can also emphasize security automation standards and practices.
- Presenting and maintaining stringent security and quality requirements will significantly reduce the number of accidental security issues introduced by developers over time.
Future Integration of DevOps and DevSecOps
As DevOps evolves into DevSecOps, we should see coding standards, security, library protocols, and legislative protocol updates become equally important.
According to a recent Gartner estimate, by 2023, 80% of firms that fail to adopt a modern security strategy will incur higher operational costs and have slower response times to attacks. Companies that cannot keep up with new security solutions will fall behind.
As automation technologies like machine learning and artificial intelligence continue to advance, we will see a shift in operations, potentially involving the introduction of new frameworks. The future of DevSecOps promises new heights in IT deployment automation, monitoring, and speed. Organizations cannot afford to treat security as an afterthought, making it crucial to incorporate DevSecOps techniques into app development immediately.
Conclusion
Should you adopt DevSecOps procedures? In our view, there is no reason not to. Even organizations without distinct IT security teams can establish one to implement many of the strategies and policies mentioned above.
DevSecOps can significantly improve the security and reliability of your software production processes without drastically extending the development lifecycle or straining corporate resources.
When you consider all the benefits and see how DevSecOps enhances the standard DevOps methodology, it’s clear that DevSecOps is a must.
Read more: How to Select a Best DevOps Service Provider