Adopting PaaS: Tips and Best Practices for Cloud Transformation
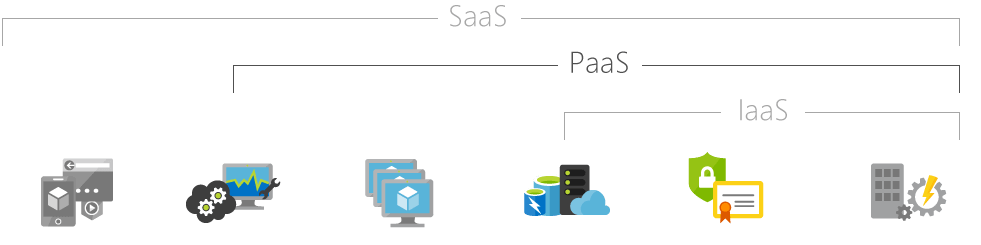
Adopting a platform-as-a-service (PaaS) delivery model dramatically boosts an organization’s ability to create services and make them available to clients and stakeholders. That is why chief information officers (CIOs) are looking to PaaS to reduce costs, produce agile services and improve the customer experience. These benefits seem like no-brainers, but it’s important to seriously consider the security implications when adopting a PaaS platform.
PaaS customers do not manage or control the underlying cloud infrastructure, which includes networks, servers, operating systems and storage. With PaaS, software patching and other vulnerability-related processes are delegated to the cloud provider. The consumer typically has no say in what gets installed. The vast majority of attacks on these systems exploit vulnerabilities for which patches are publicly available, so a good patch management strategy is the first line of defense against these attacks.
Sharing Resources in Space and Time
One of the essential characteristics of cloud computing is that resources are shared among multiple users. This is a major security concern. Consumers are afraid boundaries might break down and lead to confidentiality or integrity breaches.
Data must be as secure as possible without compromising ease of use and access. The obvious answer to this problem is encryption, but this presents a few practical challenges. For example, data needs to be unencrypted to perform searches. Performance needs could result in caching significant data in memory or even storing the encryption keys in cleartext.
Resources are shared not only in space, but also in time, meaning that the very same resource area allocated for a consumer can be reused at a later time for another consumer. Secure storage reuse and secure data disposal are critical here.
One customer’s resource usage shouldn’t affect other customers. With traditional outsourcing, isolation is achieved by maintaining dedicated physical infrastructure for each customer and wiping clean all shared computers before reuse. Some cloud providers offer resource instances that run on hardware dedicated to a single customer, causing the boundary between cloud computing and platform hosting to shrink significantly.
DDoS Response
Distributed denial-of-service (DDoS) attacks target the availability of a system or a service by saturating resources. A cloud solution’s ability to quickly respond to a changed workload — the rapid elasticity characteristic — and scale outward with demand creates a natural protection against some DDoS attacks. Due to rapid elasticity, PaaS solutions are by nature more resilient to attacks.
As a side effect, a DDoS attack that activates a spike in elasticity may involve extra unwanted costs. Whenever a cybercriminal attempts to saturate any resource, however, the rapid elasticity characteristic kicks into gear, acquiring new resources to counter the attack. The measured service characteristic may then notify the consumer that something unexpected is happening, providing an additional level of early warning.
Free PaaS offerings are often exploited to facilitate automated cloud-based attacks. The role played once by botnets is now played by sample cloud offerings: Thousands of microcloud instances can be provisioned by automated scripts and then used simultaneously to launch a coordinated DDoS attack against a small listing of targets. All the bad guys need is an application program interface (API) to provision cloud platforms, platform access to automatically install script and, eventually, a few hours of central processing unit (CPU) and network burst — just enough time to create service unavailability before being identified and taken offline.
Key PaaS Capabilities
In addition to traditional attack methods, a new phenomenon recently emerged in which cybercriminals threaten potential victims with large-scale DDoS attacks if they refuse to prepay a ransom. This is the case with DDoS for bitcoin (DD4BC), which has been active since 2014. Its rival, Armada Collective, appeared toward the end of 2015.
Security services will be a strategic market differentiator for cloud providers. A PaaS service should be able to:
- Scan and analyze mobile applications
- Scan web apps on the internet or private networks.
- Perform static analysis to scan source code for security vulnerabilities.
- Employ single sign-on capabilities.
- Drain logs over the syslog, syslog-tls or HTTPS, including all the events related to the application.
- Distinguish logs from different instances of the same application.
- Encrypt data at rest.
- Facilitate secure communication between the application and database instance.
- Discover sensitive data and stored procedures for masking sensitive data.
- Similarly, a PaaS platform should equip IT analysts with a better understanding of security policies, including practices such as source code scanning, dynamic scanning, threat modeling and penetration testing, as well as a documented process for incident management. It should help IT teams comply with industry standards regarding network security, data encryption and access control. Finally, it must enable organizations to secure data in transit, in use and at rest.
Finding the Right Solution
A cloud security platform should be designed with secure engineering practices and layered security controls across the network and infrastructure. It also needs to provide security services that application developers can use to secure their mobile and web apps.
IBM Bluemix uses infrastructure-as-a-service (IaaS) cloud services and takes full advantage of the existing Bluemix security architecture. It provides multiple, overlapping tiers of protection for your applications and data. Bluemix also adds security capabilities at the PaaS layer in three categories: platform, data and application.
Tags
Bestarion Website Admin